6 ways that G Suite helps IT admins safely use BYOD
Brad Meador
Senior Product Manager, Google Cloud
Emre Kanlikilicer
Engineering Manager, Google Cloud
Six key controls within G Suite to help keep your organization safe when using BYOD.
Contact Google Workspace Sales Team
Learn more about how Google Workspace can give your teams a better way to connect, create, and collaborate.
CONTACT USMany organizations, including Google, have moved quickly to embrace working from home. With this widespread remote work, it’s never been more important for IT admins to be certain that every device in their organization is secure, even when that device isn’t company-owned.
We pioneered zero-trust security through our BeyondCorp strategy and leverage it to offer advanced security for G Suite users to protect secure access for all devices. Admins can enforce these controls across G Suite and other corporate applications and data, ensuring consistent security and user experience across your organization.
Today, we’re laying out six key controls that IT admins can use within G Suite to help keep their organizations safe when using the bring your own device approach (BYOD). You can also review our detailed security checklist here, and learn more from our course on Managing G Suite here.
Secure mobile and desktop devices with endpoint management


BYOD devices can differ widely across an organization, with a range of OS versions, hardware modes, patch versions, and more, so it’s impossible to rely on a one-size-fits-all approach to device management. With Google endpoint management, IT admins can easily support a variety of mobile and desktop devices by enforcing measures like minimum software versions and blocking jailbroken or rooted devices, in many cases without requiring full device rights for employee privacy.
When it comes to managing mobile devices, G Suite offers basic and advanced mobile device management:
With basic mobile device management, BYOD devices are secured with baseline security features with no end user friction. Admins can enforce a passcode, get a device inventory, wipe Google accounts remotely, and even remotely install applications on Android devices.
With advanced mobile device management, admins can apply more policy controls over BYOD devices, and Android users can keep their personal data private and separate from their work data with Android Work Profiles. You can also allow and manage work apps on iOS and Android devices.
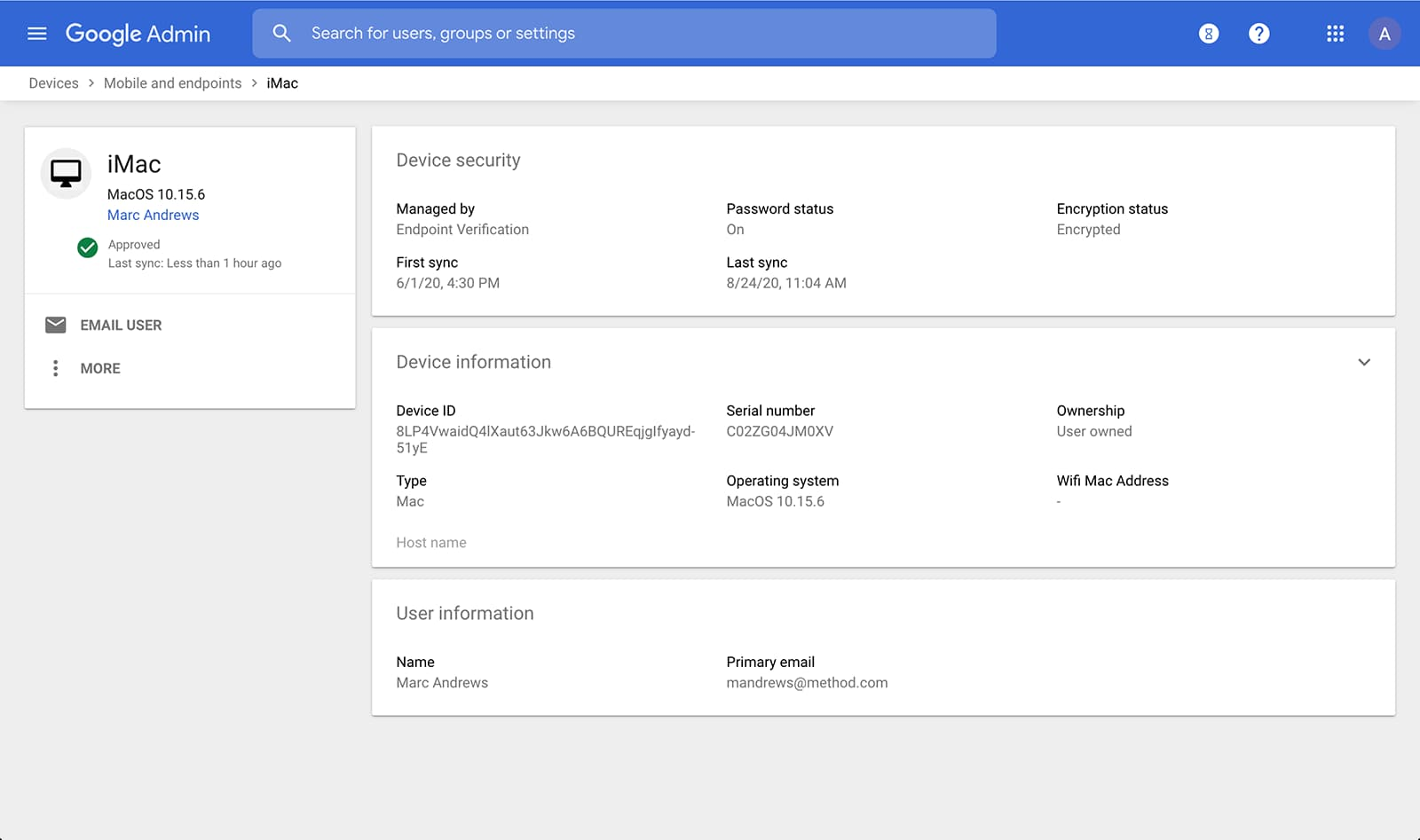
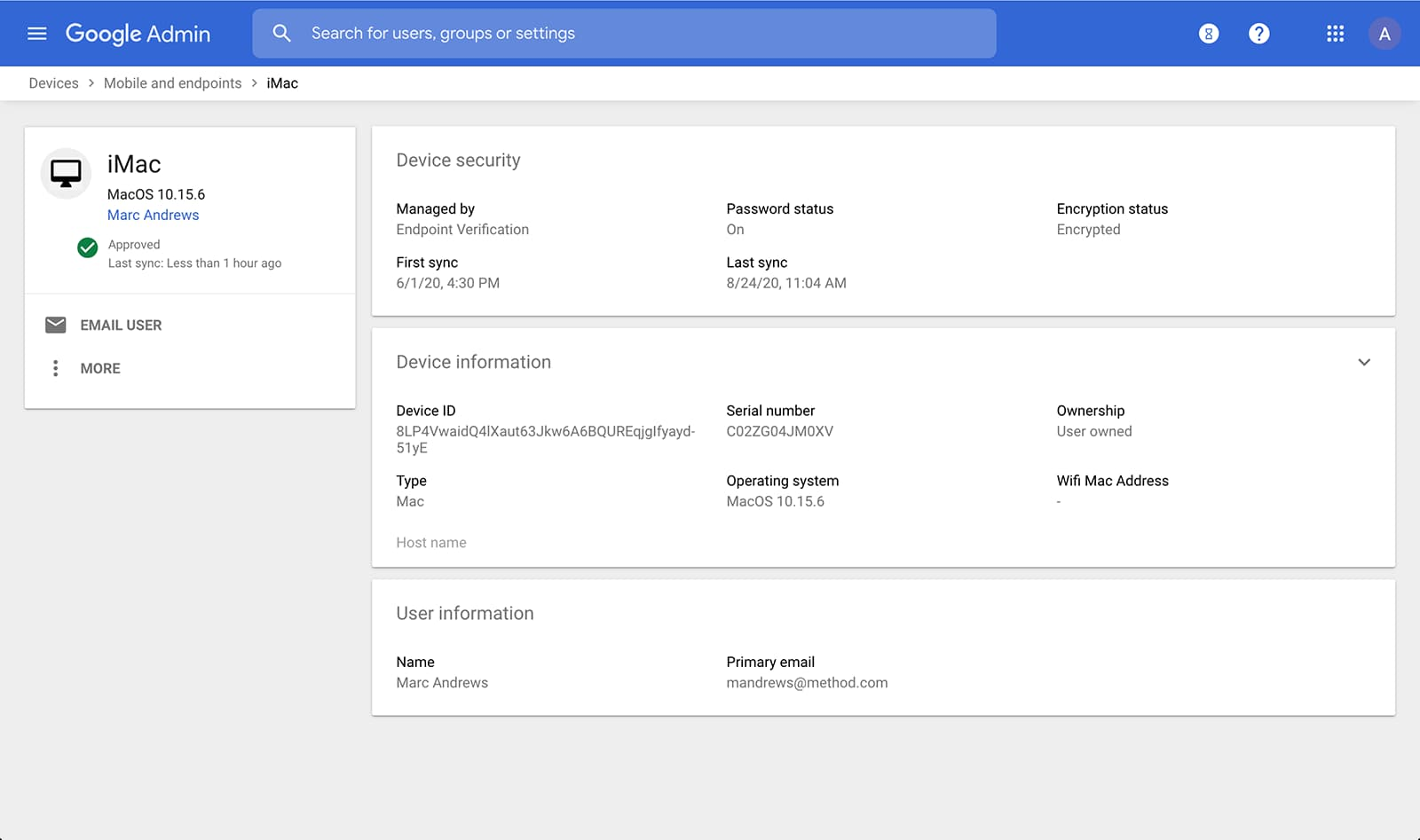
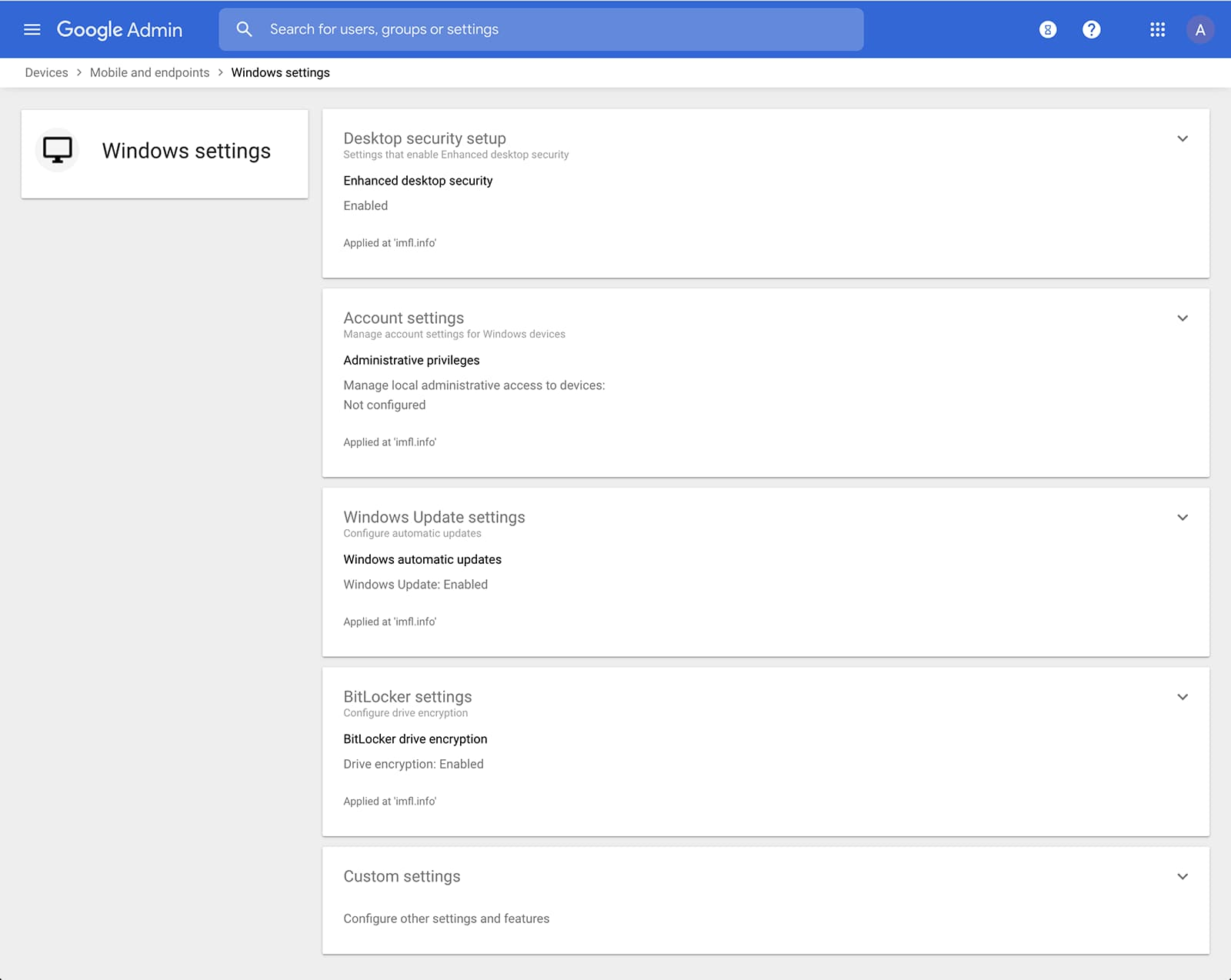
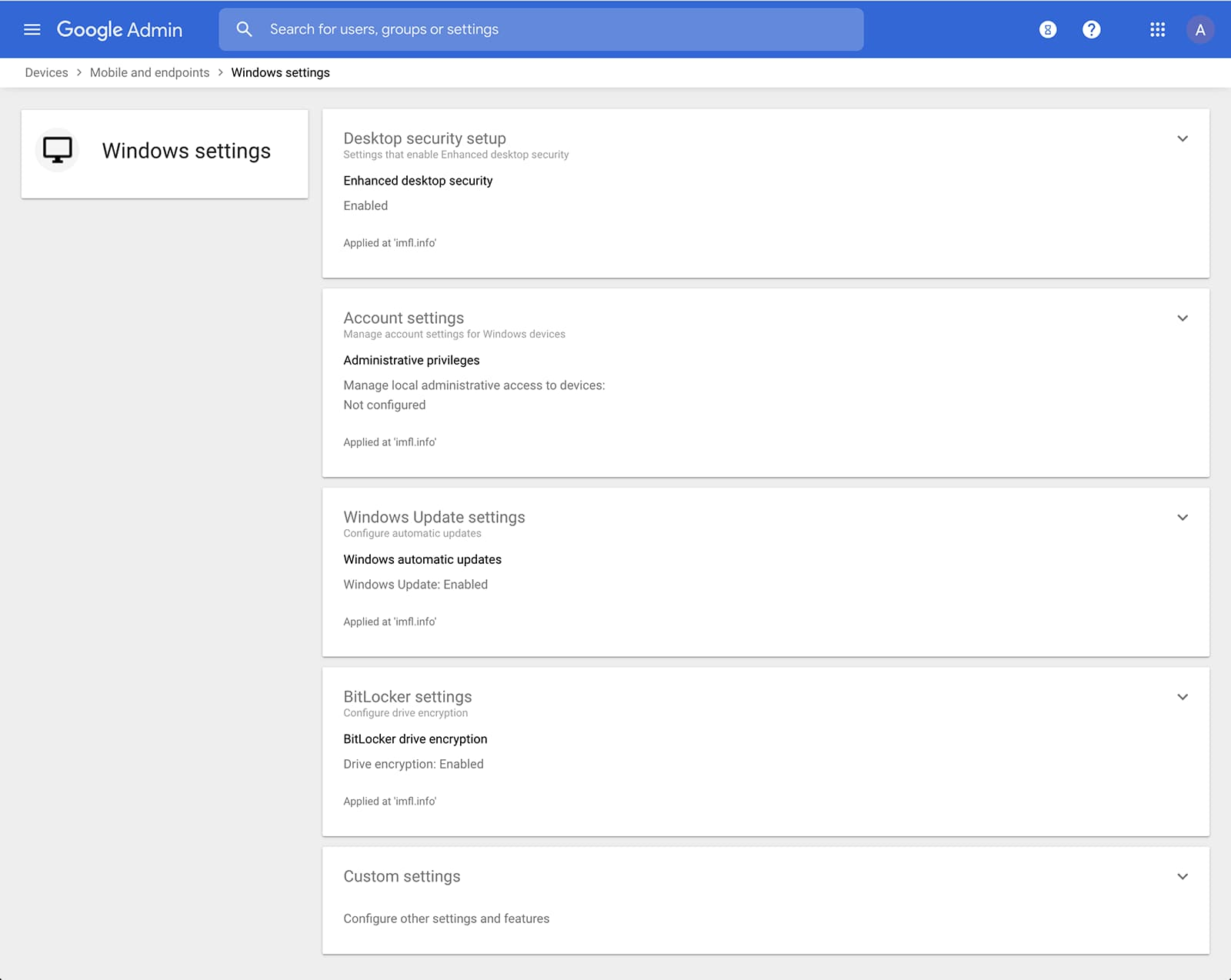
Admins can also manage and secure desktop devices with fundamental device management and enhanced desktop security for Windows. With fundamental device management, when a user logs into G Suite through any browser on a Windows, Mac, Chrome, or Linux device, that device will be automatically enrolled with endpoint management. This provides a base level of security to every desktop device that accesses G Suite data. With enhanced desktop security for Windows, admins can easily manage and secure Windows 10 devices through the admin console.
Enable secure connections without a corporate VPN using context-aware access
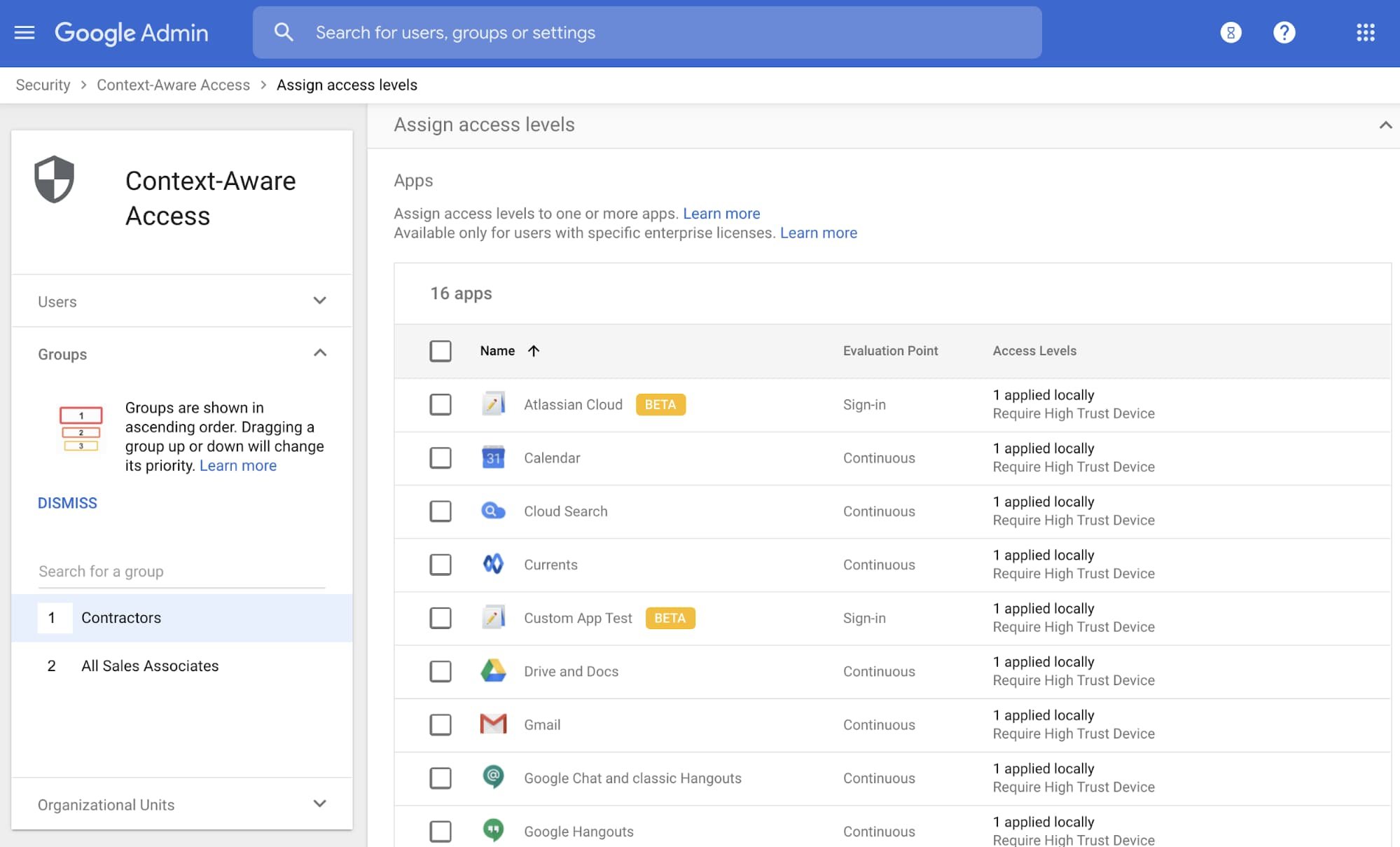
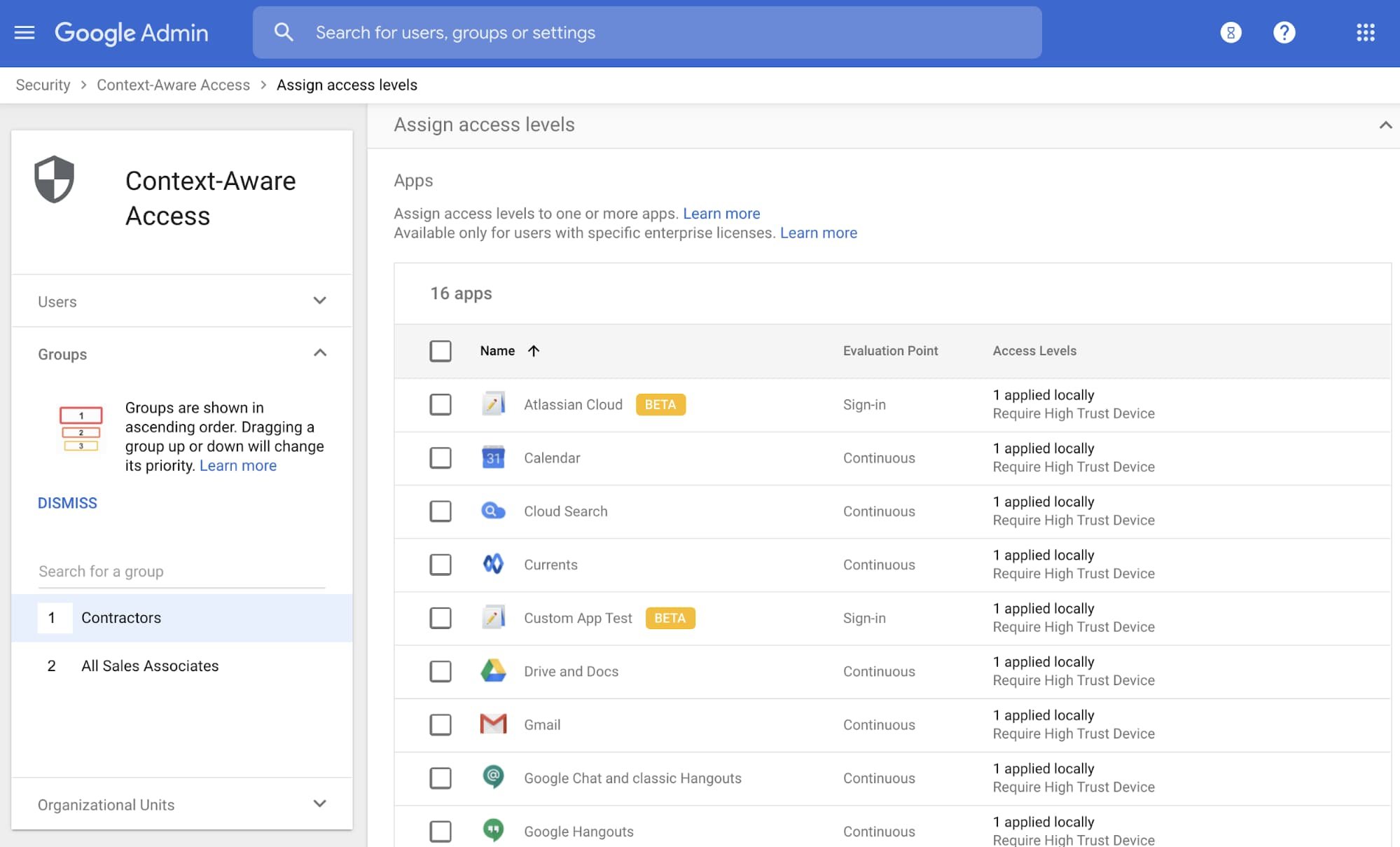
Context-aware access offers protection from unwanted access to G Suite services without the need for a VPN, and allows admins to set up different access levels based on a user’s identity and the context of the request, taking into account factors such as the country, device security status, and IP address of the request. For example, you can require BYOD devices accessing G Suite to meet encryption and password requirements, or restrict contractors from accessing G Suite from company managed Chromebooks.
Control data access with app access control


It’s important to protect all devices in your organization—corporate or BYOD—from malicious apps trying to gain access to corporate data. Using app access control, admins can take steps to prevent these apps from tricking users into mistakenly granting access to corporate data. With this feature, admins can choose which third-party apps are allowed to access users’ G Suite data by explicitly trusting, limiting, or blocking access for apps.
Enforce 2-Step Verification
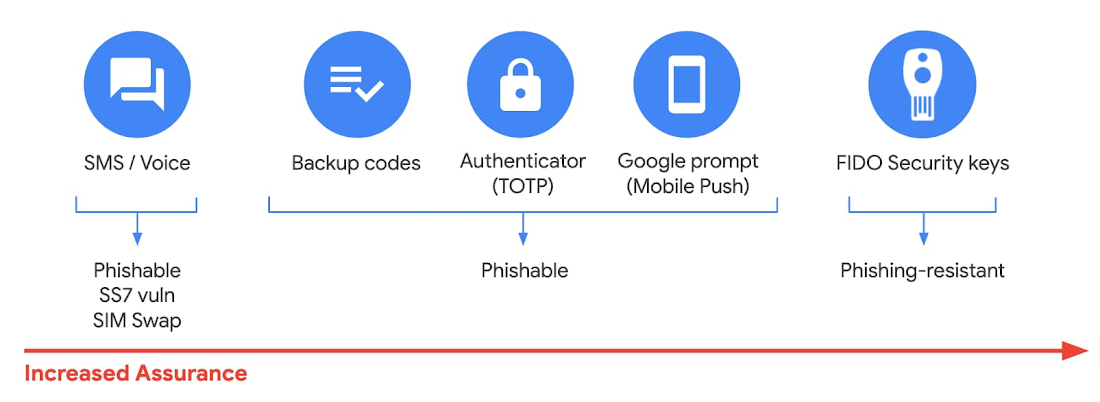
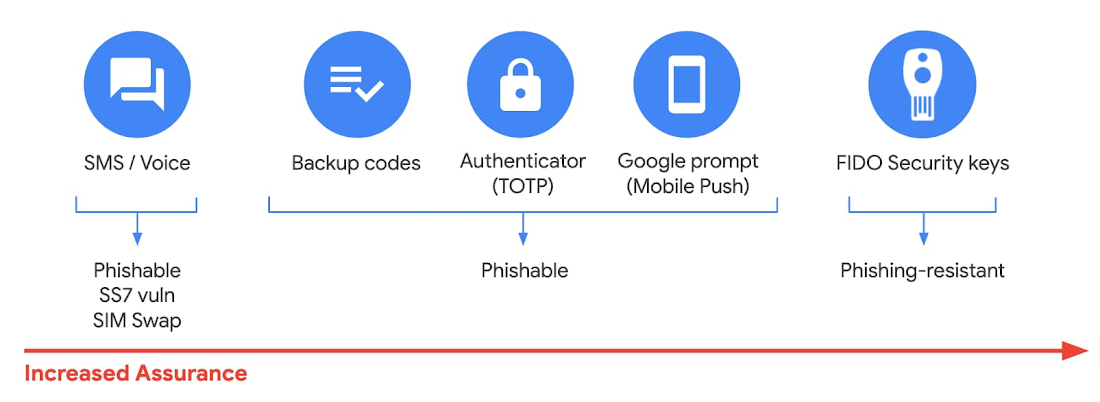
With 2-Step Verification, admins can reduce the risk of unauthorized access by asking users for additional proof of identity when signing in. And you can now use the Advanced Protection Program—our strongest protection for users at risk of targeted attacks. With the Advanced Protection Program for the enterprise, we’ll enforce a specific set of policies for enrolled users including security key enforcement, blocking access to untrusted apps and enhanced scanning for email threats
If you choose not to use security keys for any reason, you have multiple other options to enforce 2-Step Verification on BYOD devices. For Android and iOS, you can use Google prompt, Google Authenticator, text message, or phone call options for a second verification step.
Prevent data loss and leakage with data loss prevention
We know that as an admin, one of your highest priorities is to keep internal information safe and secure. That’s why we developed data loss prevention (DLP) policies to help protect sensitive information in Drive, Docs, Sheets, Slides, and Gmail from loss, misuse, or being accessed by unauthorized users. With G Suite DLP, admins can choose which types of data are sensitive and exactly how to protect them. Our controls enable easy detection of a wide variety of common info types, and administrators can supplement this with custom content detectors to meet their organization’s needs. You can also classify files in Drive automatically using DLP rules (beta) to categorize your data by sensitivity levels. DLP works on all the devices in your organization, including BYOD ones, since the protection is at the data and application level.
In addition to DLP, you can use DXP for iOS devices to restrict the copy/pasting of G Suite data to other accounts, personal or otherwise. DXP for iOS can also restrict users’ ability to drag and drop files from specific apps within their G Suite account. Similarly, you can use Google endpoint management to configure Android devices to prevent data sharing between personal and work profiles.
Make retention and eDiscovery possible on all your devices with Vault


To support your organization’s retention and eDiscovery needs, Vault enables corporate data that’s stored in G Suite and accessed by BYOD devices to be available for all your information governance needs. No matter the owner of the device, your organization’s data stored in Gmail, Drive, Chat, Groups, Voice, and Meet are accessible to Vault.
Using the zero-trust security model, the G Suite features above work together to keep your data protected and organization secure across all devices, whether they’re corporate-owned or BYOD.