Creating safer cloud journeys with new security features and guidance for Google Cloud and Workspace
Sam Lugani
Group Product Manager, Google
Rob Sadowski
Trust & Security Lead, Google Cloud
This bundle of new security features and resources will help Google Cloud customers secure their environments.
Try Google Workspace at No Cost
Get a business email, all the storage you need, video conferencing, and more.
SIGN UPOne of the core benefits of using cloud technology to help modernize your security program is the ever-growing set of provider capabilities that you can use to protect your users, applications, and data. As part of our commitment to be our customers’ most Trusted Cloud, we’re constantly adding new security features to Google Cloud and Google Workspace, as well as helpful guidance on how to solve security challenges and improve your security posture with the help of our tools. We've got a bundle of new security features, whitepapers and demos to announce today, which can all help to create safer cloud journeys with Google:
Customize your application’s authentication flows using Identity Platform
Identity Platform is our customer identity and access management solution that allows you to add IAM functionality to your applications. We are excited to announce the general availability of blocking functions, a feature that allows you to customize your application’s identity flows. Blocking functions work as a hook and trigger system, allowing you to set hooks for certain user authentication events using Node.js code in Google Cloud Functions and trigger functions in response to these events.
Here are few examples of situations where blocking functions are particularly useful:
Your application allows email/password based self-registration for users, but you want to block users with bad email domains from signing up to your app.
When a user signs-up or signs-in to your application, you want to assign them a role such as `admin` or `premium_user` and use it to control privileged access to your app
You want to use additional information found in the OAuth token issued by the federation Identity Provider (ID, Access, and Refresh tokens) for additional access enforcement to your database, such as country code, geo-location or other such claims about the user
Update or enrich the user profile with additional information you progressively profiled from the user, such as their phone number, location, language preference etc., and save them to the user record in the Identity Platform database.
Blocking functions run synchronously and will block the underlying events from completing until the function responds—allowing you to modify authentication events in real-time.


Learn more about Identity Platform and blocking functions by visiting the documentation page.
Cloud DLP Sensitive Document Analysis
Sometimes just knowing the format of a piece of data can tell us that the document it's part of is sensitive; source code, account numbers, or financial documents for example. Cloud Data Loss Prevention (DLP) now offers a new set of AI/ML powered document classifiers that can help you identify sensitive document types; sensitive document infoTypes.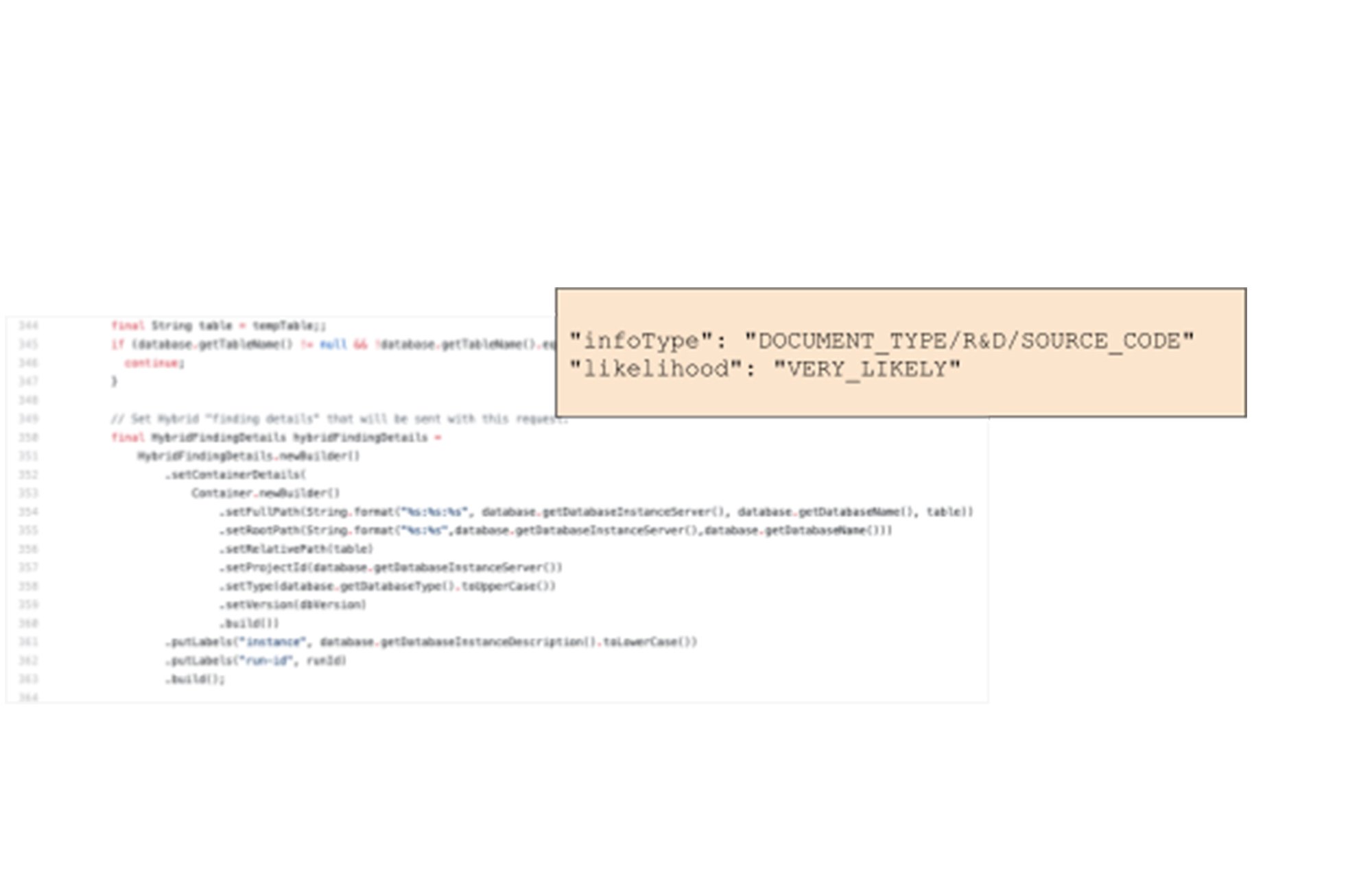
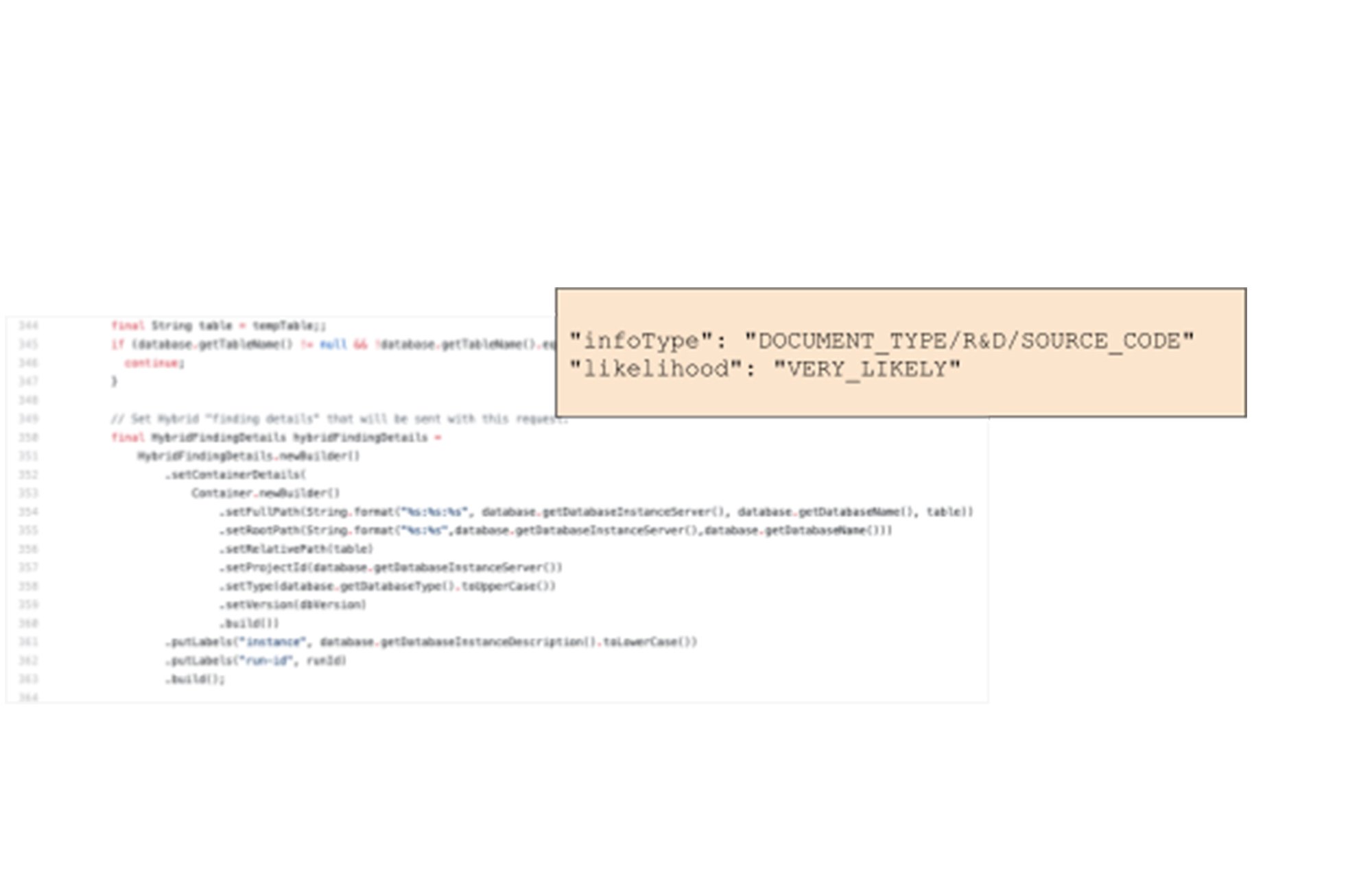
Used alone or in combination with personally identifiable information (PII) or enterprise credentials and secrets inspection, this new feature of Cloud DLP can help you discover, better understand, and protect your sensitive data. See the DLP product page and review our DLP UI demo to learn more and get started.
Cloud EKM supports additional services (Cloud SQL, GKE and others)
In early 2020 we launched Cloud External Key Manager (Cloud EKM), the industry’s leading Hold-Your-Own-Key (HYOK) product. Using Cloud EKM, the keys used to protect your data stored and processed in Google Cloud are completely hosted and managed outside of Google Cloud infrastructure. Cloud EKM initially launched with support for BigQuery and GCE/PD; we’re excited to expand support for Cloud SQL, GKE, Dataflow Shuffle, and Secret Manager, with CMEK support currently in beta. Cloud Spanner is now also supported by CMEK. You can now have even more control over how you protect your data-at-rest in those services. See the Cloud EKM documentation for more information.
VPC-SC directional policies
As organizations plan cloud migrations, they often find that familiar security strategies, such as using firewalls to segment applications aren’t applicable when those apps are re-architected to take advantage of managed cloud services like databases or storage buckets. With VPC Service Controls (VPC-SC), administrators can define a security perimeter around Google-managed services to control communication to and between those services. Using VPC-SC, you can isolate your production GCP resources from unauthorized VPC networks or the internet, and isolate both production GCP resources and production VPC networks from unauthorized GCP resources. But what if you need to transfer data between isolated environments that you’ve set up?
VPC-SC directional policies is a new secure data exchange feature that allows you to configure efficient, private, and secure data exchange between isolated environments. Policies can be applied on ingress or egress from a VPC Service Controls perimeter and can be configured for existing perimeters or included when a new perimeter is created.
It further improves context-based access control for GCP resources where context can include network origin (IP address or VPC network), identity type (service account or user), identity, and device attributes.
With VPC-SC directional policies, you can:
Efficiently exchange data across organizations with fine-grained direction controls to minimize data exfiltration risks.
Constrain identity types or identities that can be used given a source network, IP address or device for both ingress and egress
Ensure that clients in less privileged segments do not have access to GCP resources in more privileged segments; while allowing access in the other direction.
Check out the documentation to see how to take advantage of this new capability.
New whitepapers on Certificate Authority (CAS) and External Key Manager (EKM)
We continue to provide documentation to help customers and prospects understand how to use our cloud security services and how to simplify deployment for real-world use cases. Today we are releasing two new whitepapers about our Certificate Authority Service that serve those needs.
“Scaling certificate management with Google Certificate Authority Service” (written by Andrew Lance of Sidechain, Anton Chuvakin and Anoosh Saboori of Google Cloud) focuses on CAS as a modern certificate authority service and showcases key use cases for CAS. “How to deploy a secure and reliable public key infrastructure with Google Cloud Certificate Authority Service” (written by Mark Cooper of PKI Solutions and Anoosh Saboori of Google Cloud ) covers security and architectural recommendations to organizations for the use of the Google CAS and describes critical concepts to securing and deploying a PKI based on CAS.
Also, as we shared in our blog “The cloud trust paradox: To trust cloud computing more, you need the ability to trust it less” and then in “The cloud trust paradox: 3 scenarios where keeping encryption keys off the cloud may be necessary”, we’ve been working on letting customers use Google Cloud without trusting us with their encryption keys. To help further this initiative, we are releasing a new resource focused on Cloud External Key Manager (Cloud EKM), our technology for Hold Your Own Key (HYOK). The whitepaper is focused on the origin of the idea, the functionality, architecture and use cases for Cloud EKM. It is written by Andrew Lance of Sidechain, and Anton Chuvakin of Google Cloud.
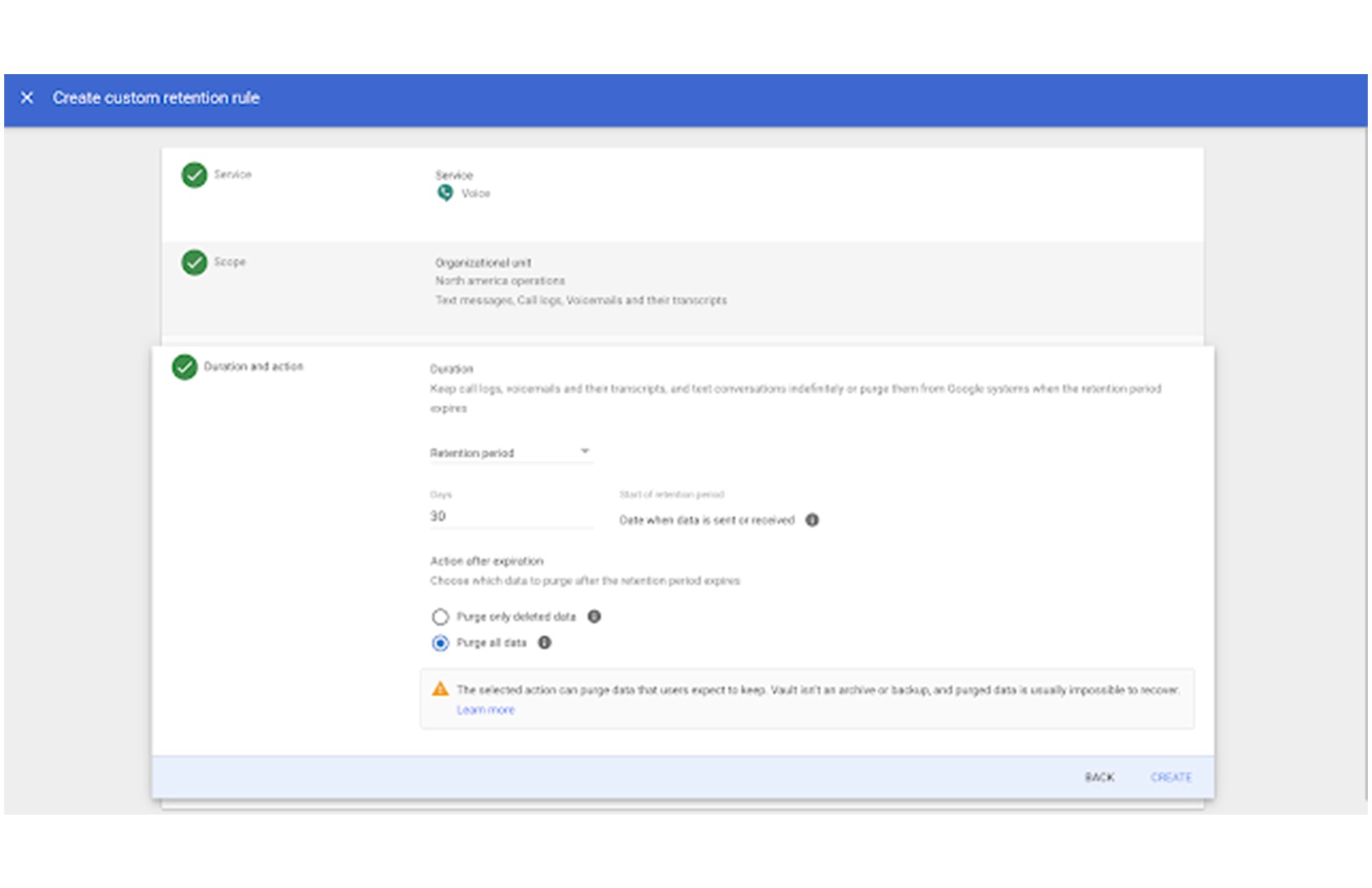
Enhancements to Vault for Google Workspace
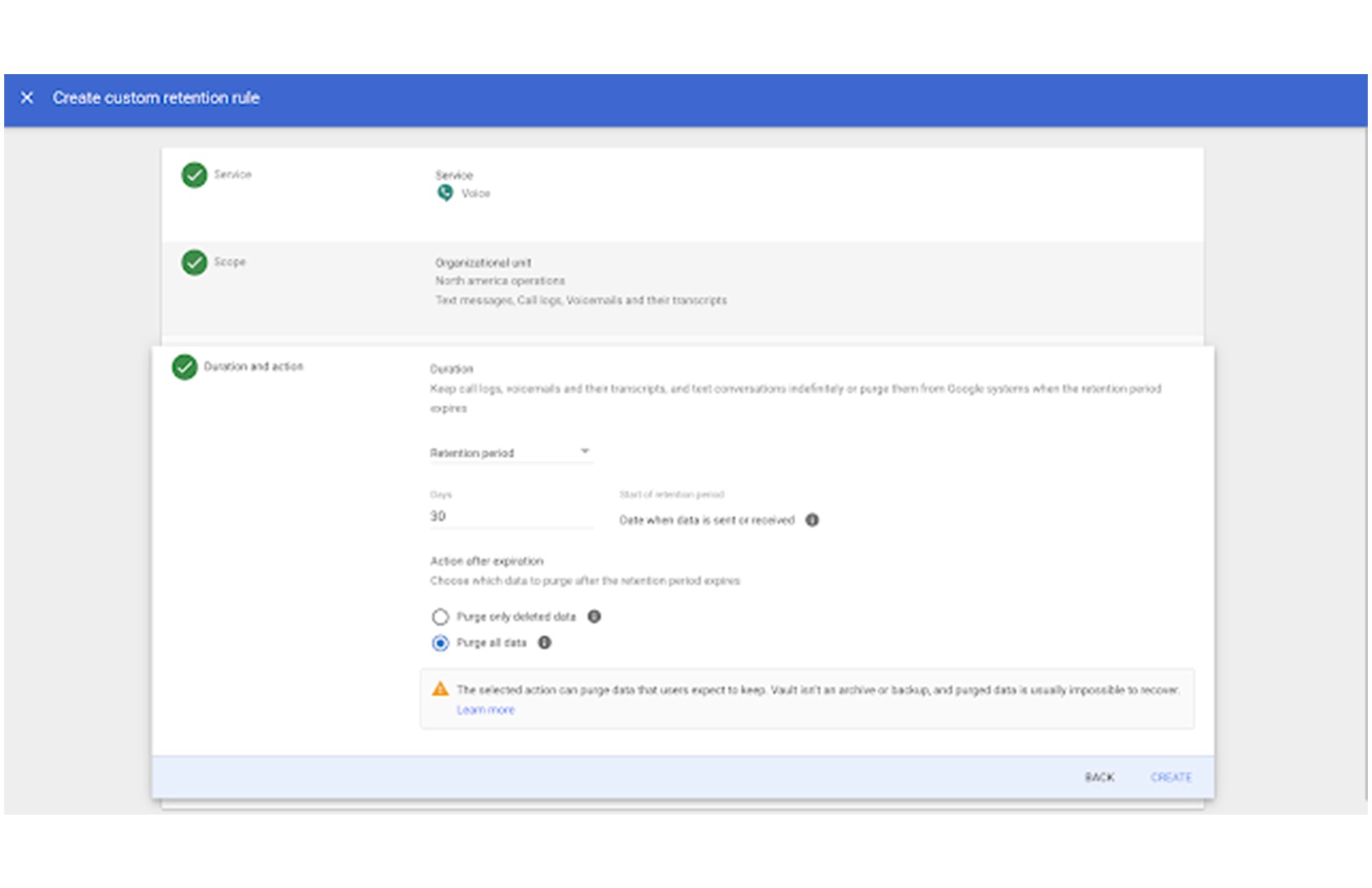
Google Vault is a powerful information governance and eDiscovery tool for Google Workspace. Vault got a new look late last year, with a redesigned interface that makes it easier and faster to navigate through the tool. Some enhancements that can help you be more productive in Vault include new sortable, filterable tables for custom retention rules, holds, and search results, and step-by-step flows with added tooltips when you set up retention rules and holds.

Next, Vault now supports Google Voice data, which means you can use Vault to retain, hold, search, and export Google Voice data including text messages, call logs, voicemails, and voicemail transcripts. By expanding Vault’s coverage to Google Voice, customers can use Vault’s information governance, eDiscovery, and auditing capabilities to help meet their regulatory and legal obligations for that data.
New Google Cloud Security Showcase videos
The Google Cloud Security Showcase is a video resource that’s focused on solving security problems and helping you create a safer cloud deployment. With more than 50 step-by-step videos on specific security challenges or use cases, there’s something for every security professional. We’ve added 4 new use-case based videos this month:




These announcements show how we continue to work to be your most Trusted Cloud. To learn more about Google Cloud’s security vision and understand how to implement cutting-edge security technology in your organization, tune into the latest installment of our Google Cloud Security Talks on May 12th.



